Software Conax Decrypter
Posted : adminOn 3/5/2018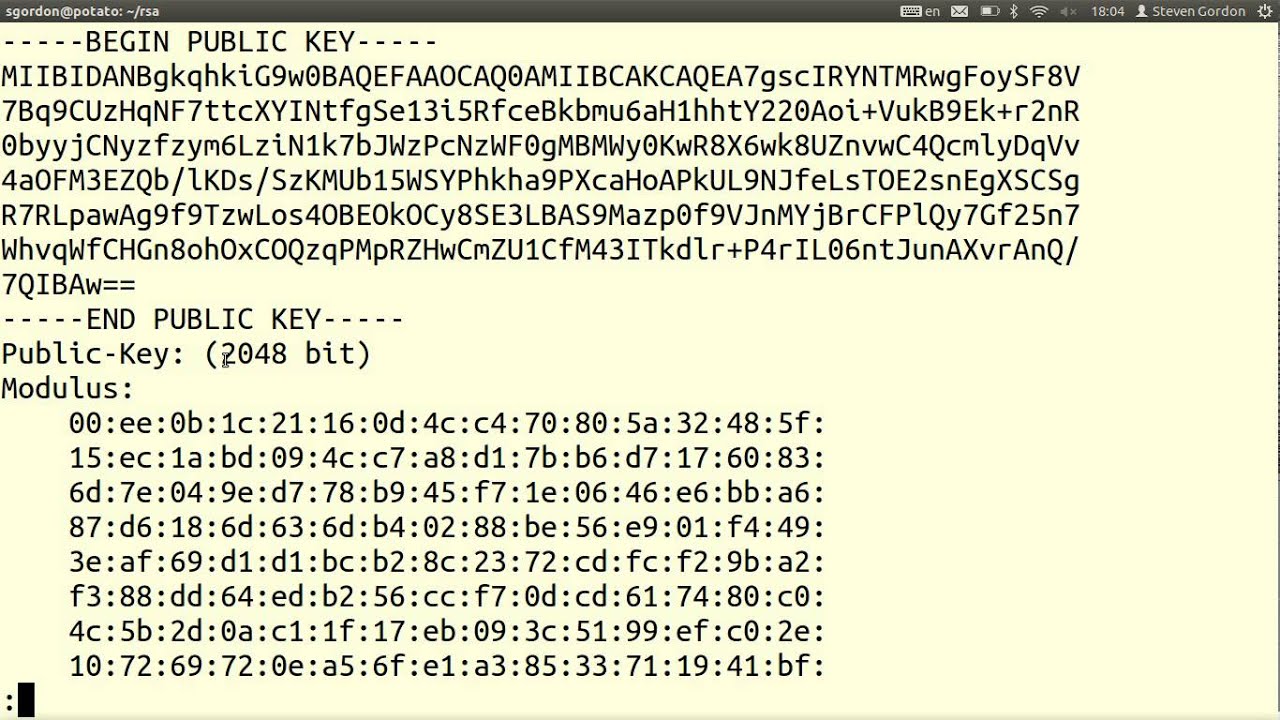
Jun 24, 2006. Joined: Jun 24, 2006. Likes Received: 0. Trophy Points: 0. My Satellite Setup: Don know. My Location: India. Then can I watch any other encryption type channels without a viewing card i e other than conax encrypted?? Is there any software for the receiver to do so? Cakewalk Express 8 Free Download. ? Defaultuser, Jun 25, 2006. V --version Show program version. Examples ======== To get a quick start here are some example command lines. The default CA system is set to CONAX, you can change it using --ca-system parameter, see man page or program help for more options. Examples: # Decrypt multicast stream from 239.0. Aug 21, 2017. It will provide the market with a highly secure Cardless solution utilizing a unique combination of hardware and software security resulting in a high level of. SmarCAM is a module relying on the DVB Common Interface (DVB-CI) and CI Plus standards that plugs directly in the digital TV to decrypt premium. Typically, a legitimate smart card is attached to a host digital television receiver, which is equipped with software to share the decrypted 64-bit 'control word' key over a computer network, such as the Internet. Once a client receives this key, they can decrypt the encrypted content as though they were using their own.
Over the last couple of days a small furore has erupted a News Corp subsidiary,, has been hacking the pay-TV smartcards of News Corp’s competitors, and even News Corp’s own companies – allegations that NDS. I’m not going to speculate on the reasons why a supplier of – the technology that allows paid-TV providers to restrict access to their broadcasts – would want to undermine the security of their own product; but I am going to discuss how such systems work, and how secure they are. A Conditional Access Module (CAM) is a combination of encryption keys, smartcards and electronics and computer code inside a satellite or cable-TV receiver (or “decoder”). The pay-TV provider encrypts the digital signal sent to the subscriber with an encryption key. The subscriber plugs a smartcard into his/her decoder, which decrypts the signal so programs and films can be displayed on the screen. Some decoders have the smartcard built-in already, so there is no external slot. The is a plastic card with a chip - much like a modern credit card.
You can see electrical contacts on the chip. When the card is inserted, the chip is plugged into the decoder, allowing the CAM to get the decryption key. Other information is also stored on the chip – subscriber ID, subscription details, billing details, censorship filters and so on. We don’t really know what’s there unless we hack into the chip, because it’s all kept secret. Each chip will have it’s own non-volatile memory (requires no battery), computer programs and a small (CPU). The security of the system depends on a few things: • secrecy of the encryption algorithm • secrecy of the keys • secrecy of the hardware. So let’s start with the.
An algorithm is a recipe for doing something – in this case, for scrambling and descrambling the digital signal. Some CAM providers write their own algorithm, and depend on it remaining a secret.
That’s a bit like hiding your door key inside a brick or under a flower pot – once the secret (that the key is in the brick) is discovered, you have no security. Works this way.
Ford Cargo 0913 Manual Lawn more. A much better approach is to keep the key with you (a secret key). Everybody knows how your door security works (you put the right key in the lock and turn), but that only works if you have the key. If your lock (algorithm) is faulty, you’ll find out quickly enough and replace the lock. Of course, Pay-TV subscribers would have to remember the key, and have to enter it into their decoder - very inconvenient, but very safe. Foxtel uses CAMs. These use encryption - a reasonably complex encryption algorithm that’s difficult to crack without employing lots of supercomputers. 3DES is a known algorithm - it has been tested for years and, if implemented correctly, will be safe.